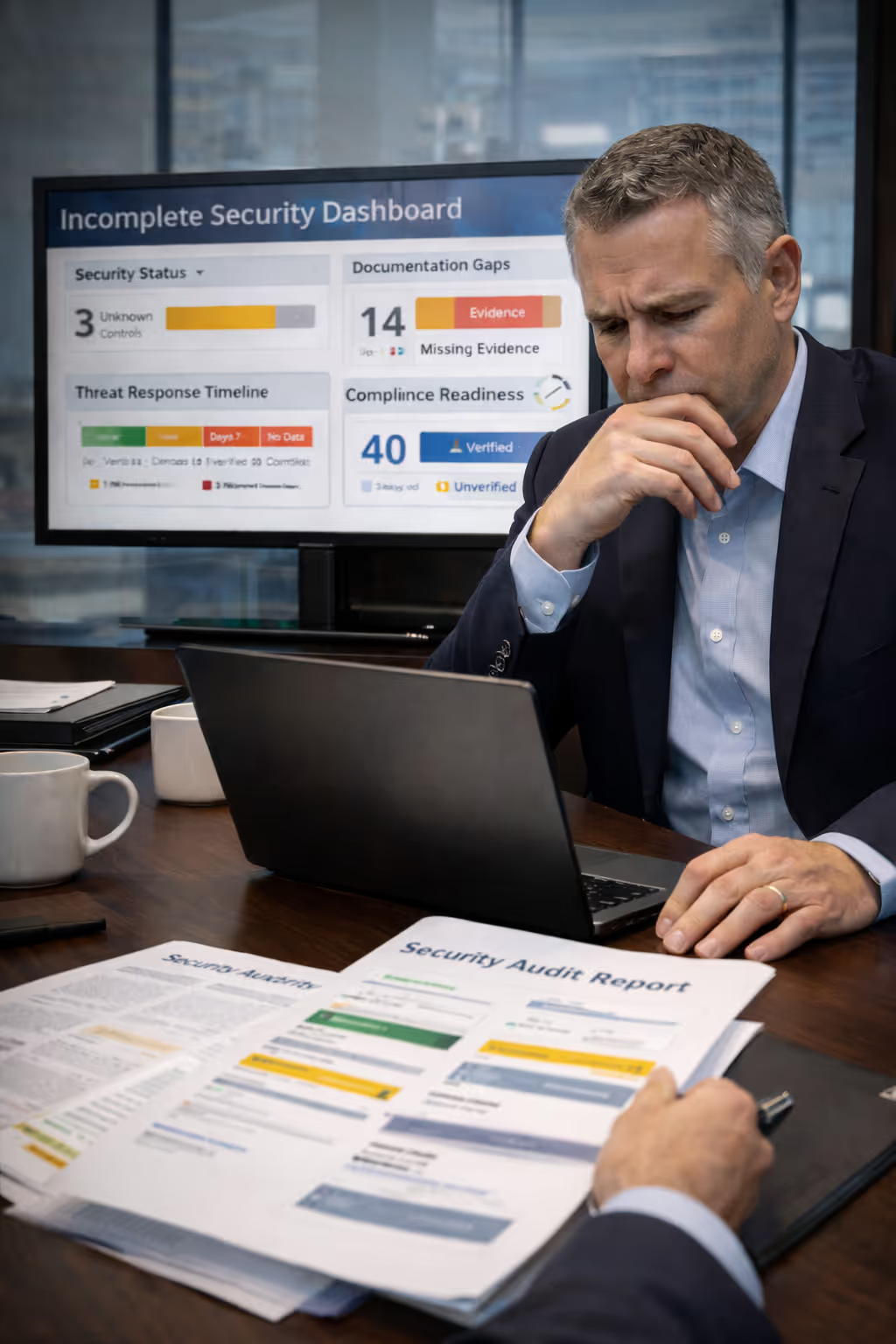
Built for Lean Teams in Regulated Environments
Desert Shield supports mid-market organizations that need enterprise-grade cybersecurity and compliance discipline without enterprise overhead.
We work best with security leaders who are accountable for uptime, audit readiness, and risk exposure, but do not have the luxury of large internal teams.
Organizations We Serve Best
100–2,000 employees
Limited internal IT/security staff
Regulatory or insurance oversight
Multi-vendor security environments
Executive accountability for risk decisions
Less Effective For
Organizations that prefer to manage dozens of disconnected point tools internally.

.avif)






.avif)